MPCVault and Rain are thrilled to announce the launch of the MPCVault Card, a cutting-edge payment solution designed to help businesses seamlessly spend USDC anywhere Visa is accepted. This partnership brings together MPCVault’s state-of-the-art non-custodial wallet technology and Rain’s innovative digital payment infrastructure, making it easier than ever for businesses to use crypto for real-world transactions.
USDC Payments Without Off-Ramping
With the MPCVault Card, businesses no longer need to go through traditional off-ramping processes to access fiat. Instead, they can use their USDC holdings to pay for online and in-store purchases instantly. Whether it’s covering operational expenses or managing team spending, the card offers a frictionless way to integrate stablecoins into everyday transactions.
Built for Businesses: Multi-User & Customizable Controls
Designed with businesses in mind, the MPCVault Card comes equipped with advanced corporate features, including:
- Customizable spending templates to streamline expense management
- Unique spending limits per user for greater financial control
- Seamless team finance management for businesses of all sizes
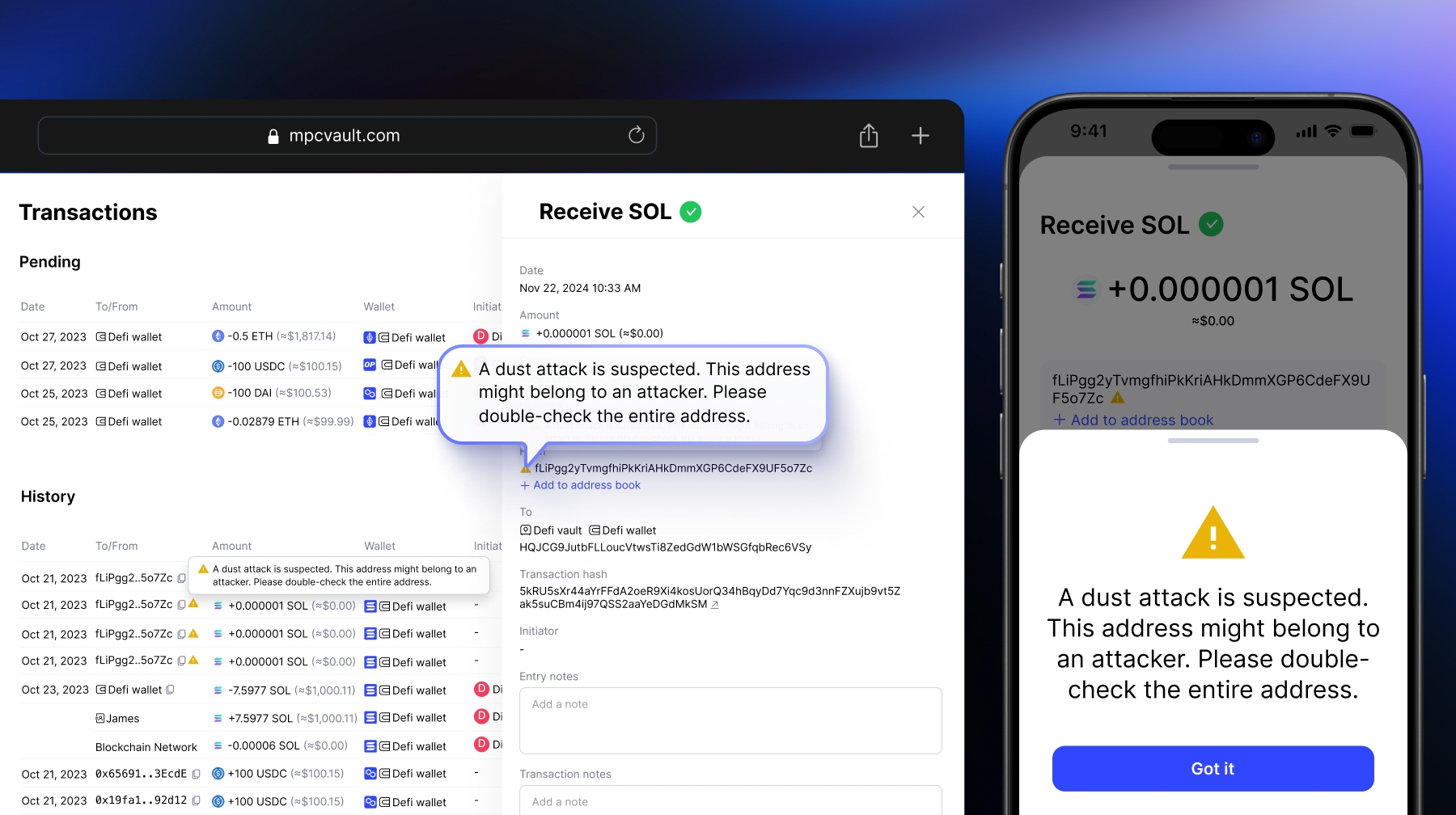
Secure & Trusted by Leading Crypto Enterprises
Security is at the core of MPCVault’s technology. The platform utilizes multiparty computation (MPC) to ensure unparalleled protection of digital assets. With over 1,000 companies relying on MPCVault to process $1.5 billion onchain every week, the company has become a trusted partner for exchanges, venture capitals, hedge funds, and trading desks worldwide.
A New Era for Stablecoin Payments
The launch of the MPCVault Card is just the beginning. As MPCVault expands access to more businesses, the initiative will play a crucial role in driving the adoption of stablecoins in global payments.
Want to be among the first to access the MPCVault Card? Apply now:
MPCVault Card Application
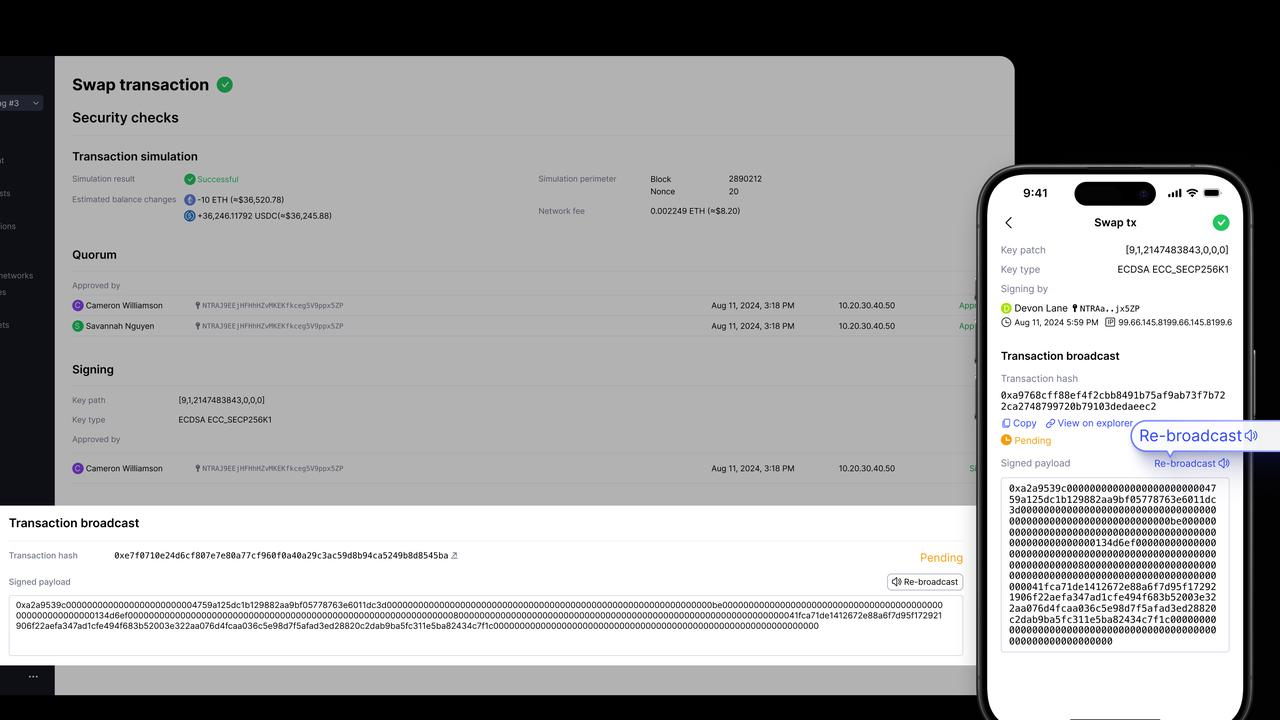
How the card works