With the burgeoning prominence of cryptocurrencies, Ethereum has emerged as a powerhouse for investors, developers, and everyday users seeking to take part in the digital financial revolution. Integral to this landscape, however, is the pressing need for cybersecurity vigilance. The unfortunate reality is that as Ethereum's ecosystem expands, so does the craftiness and prevalence of ETH scammers. In this comprehensive guide, we'll equip you with the knowledge to identify, avoid, and protect yourself against the most common Ethereum scams circulating today. The cliché 'knowledge is power' has never been more pertinent than in the realm of cryptocurrency safety.
Understanding Ethereum and Its Significance in Cryptocurrency
Ethereum, the blockchain-based platform, has not only introduced its native currency, Ether (ETH), but it has also paved the way for decentralized applications (DApps) through smart contracts. Unlike Bitcoin, Ethereum's utility isn't limited to a peer-to-peer currency; it's the foundation layer for a burgeoning ecosystem of digital assets and applications that are revolutionizing multiple industries. Its potential for creating a decentralized internet, or Web3, has driven ETH to become one of the most valuable and widely recognized cryptocurrencies in the world.
But as the potential for profit attracts more participants, it also draws the attention of opportunistic scammers. These malicious actors craft sophisticated schemes to exploit the unwary, often capitalizing on the complex and sometimes opaque nature of blockchain technology.
For instance, take the notorious "DAO Attack," where in 2016, hackers exploited a vulnerability in a decentralized autonomous organization (DAO) built on Ethereum, siphoning off an equivalent of $50 million in ETH. It stands as a stark reminder that the cutting-edge tech underpinning Ethereum does not exempt it from the age-old threat of scams.
Another more recent example is the rise in DeFi-related scams, where fake decentralized finance projects lure investors with the promise of high returns, only to drain the pooled funds through 'rug pull' tactics. These are sobering demonstrations of the risks that come with the Ethereum's expansive and largely unregulated frontier.
Common Types of Ethereum Scams
As investors flock to Ethereum in search of innovative financial solutions, the landscape becomes rife with various intricate scams. Awareness is the first line of defense, so let's examine some of the most common types of Ethereum scams that every crypto enthusiast should be wary of.
Phishing Scams
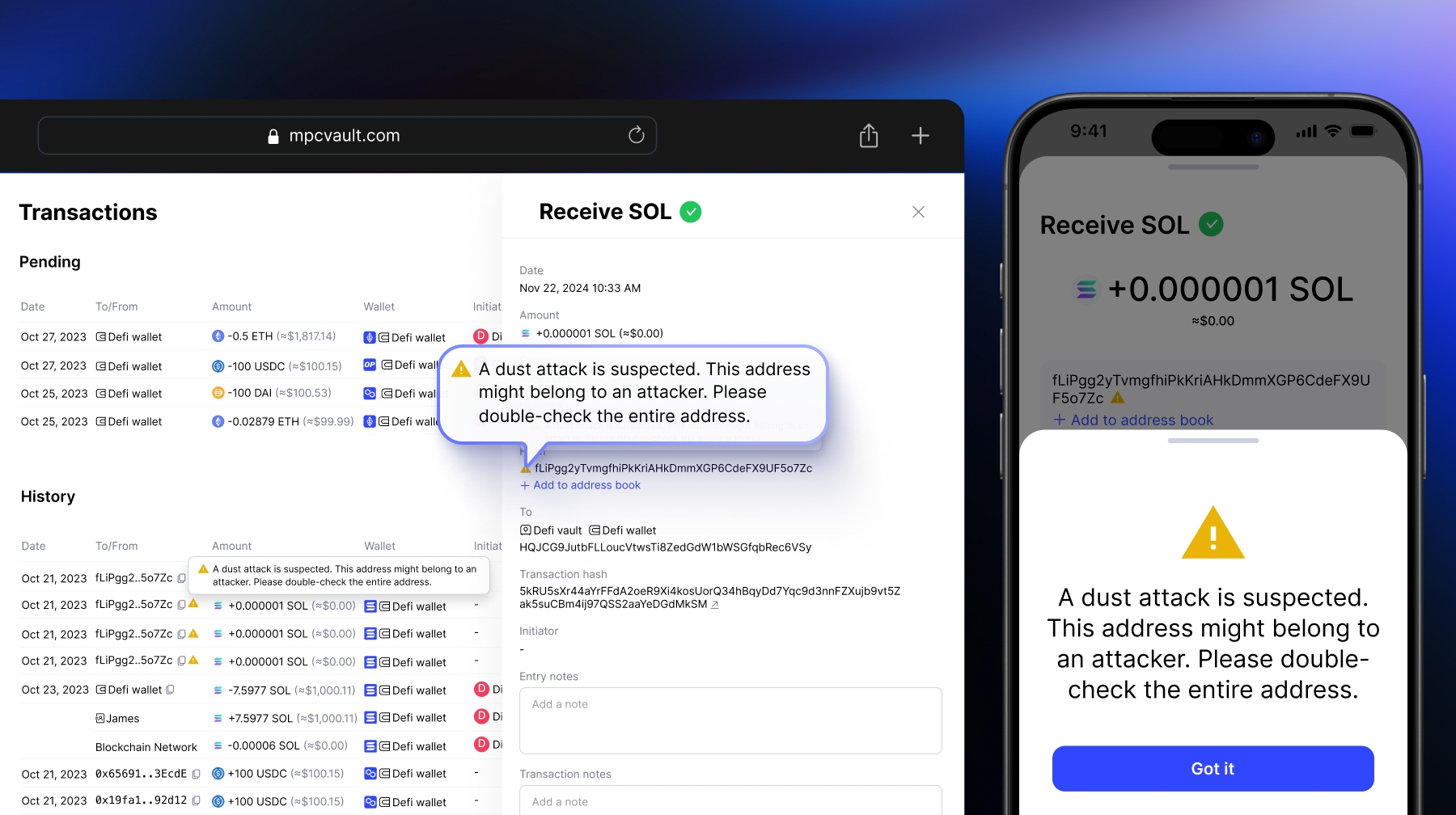
Phishing attempts are as old as the internet, but in the Ethereum world, they've taken a nefarious turn. A typical phishing scam involves tricking an individual into providing their private keys or seed phrases under the guise of a legitimate request. Often, these come in the form of fake websites, emails, or even social media messages pretending to be from reputable sources.
For example, a user might receive an email that appears to be from a well-known Ethereum wallet or exchange, asking them to "verify" their account details. This scam has claimed numerous victims, leading to the loss of vast amounts of ETH as scammers gain access to their wallets.
Fake ICOs and Token Sales
The initial coin offering (ICO) boom on the Ethereum blockchain provided a fertile ground for fake ICOs and token sales. Scammers create convincing websites and whitepapers for non-existent projects, complete with fake team member profiles, to solicit funds from unsuspecting investors. A notorious incident was the "My Big Coin" scam, where the operators fabricated a fake cryptocurrency and defrauded investors out of $6 million.
Ponzi and Pyramid Schemes
Ethereum's decentralized nature has regrettably been exploited for traditional Ponzi and pyramid scheme models. These scams promise returns from the investments of new participants to earlier investors, creating a cycle that inevitably collapses. The fall of the "DavorCoin" project, which was essentially an Ethereum-based Ponzi scheme, left many investors in financial ruin.
Impersonation and Giveaway Scams
Ethereum's community has also seen a surge in impersonation and giveaway scams, where scammers pretend to be famous figures or brands offering free ETH. One well-documented case involved fraudsters impersonating Elon Musk on Twitter, convincing users to send them a small amount of ETH in exchange for a larger return that never materializes.
Being aware of these deceptive strategies can not only prevent financial loss but also foster a safer Ethereum ecosystem for all. Always verify the authenticity of any investment opportunity and approach unsolicited offers with a high degree of skepticism.
What to Do If You've Been Scammed with ETH
Falling victim to an Ethereum scam is a distressing experience, but taking swift action can help mitigate the damage. If you find yourself in the unfortunate position of having been scammed, here's what you need to do next.
Firstly, isolate and secure any remaining assets. Move your funds to a new wallet with an unrelated seed phrase to prevent any further unauthorized access. Report the scam to the Ethereum community forums and social media to alert others of the malicious scheme and potentially get advice on further steps.
Don't hesitate to contact law enforcement and provide them with all the details of the scam, including transaction histories and any communication you've had with the scammers. While recovering lost funds is challenging, involving authorities is critical for investigation and helps them build a case against cybercriminals.
Additionally, file a report with relevant online fraud bureaus and the Federal Trade Commission (FTC) in the United States, or your local governing regulatory authority if you're based internationally. Blockchain forensics firms can sometimes assist in tracking the movement of stolen funds, although this is often a service with associated costs.
When it comes to scams, prevention is always better than cure. Staying informed and adopting rigorous security measures are your best defense against the rising tide of Ethereum-related scams.